CVE-2026-24858
Fortinet Multiple Products Authentication Bypass Using an Alternate Path or Channel Vulnerability - [Actively Exploited]
Description
An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18, FortiProxy 7.6.0 through 7.6.4, FortiProxy 7.4.0 through 7.4.12, FortiProxy 7.2.0 through 7.2.15, FortiProxy 7.0.0 through 7.0.22, FortiWeb 8.0.0 through 8.0.3, FortiWeb 7.6.0 through 7.6.6, FortiWeb 7.4.0 through 7.4.11 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices.
INFO
Published Date :
Jan. 27, 2026, 8:16 p.m.
Last Modified :
May 12, 2026, 6:47 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Fortinet FortiAnalyzer, FortiManager, FortiOS, and FortiProxy contain an authentication bypass using an alternate path or channel that could allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Unknown
Please adhere to Fortinet's guidelines to assess exposure and mitigate risks. Check for signs of potential compromise on all internet accessible Fortinet products affected by this vulnerability. Apply any final mitigations provided by the vendor as soon as they become available. For more information please see: https://fortiguard.fortinet.com/psirt/FG-IR-26-060 ; https://www.fortinet.com/blog/psirt-blogs/analysis-of-sso-abuse-on-fortios ; https://nvd.nist.gov/vuln/detail/CVE-2026-24858
Affected Products
The following products are affected by CVE-2026-24858
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 6abe59d8-c742-4dff-8ce8-9b0ca1073da8 | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update FortiAnalyzer to version 7.6.6 or later.
- Update FortiManager to version 7.6.6 or later.
- Update FortiOS to version 7.6.6 or later.
Public PoC/Exploit Available at Github
CVE-2026-24858 has a 16 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-24858.
| URL | Resource |
|---|---|
| https://fortiguard.fortinet.com/psirt/FG-IR-26-060 | Vendor Advisory |
| https://cert-portal.siemens.com/productcert/html/ssa-975644.html | Third Party Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-24858 | US Government Resource |
| https://www.fortinet.com/blog/psirt-blogs/analysis-of-sso-abuse-on-fortios | Mitigation Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-24858 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-24858
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Distributed honeypot intelligence platform with LLM-powered adaptive deception, RL engagement scoring, automated SIEM rule generation (Suricata/Sigma/YARA), ML anomaly detection, and C2/covert channel detection. 55M+ events from 22K+ IPs across 122 countries. Rules auto-synced every 6h.
Shell Dockerfile Python YARA
None
Shell Python
Security Runbooks
CVE-2026-24858 - Administrative FortiCloud SSO authentication bypass
exploit fortigate fortigate-firewall fortnite python python3 scanner
Python
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
None
While Fortinet's January 27, 2026 mitigation for **CVE-2026-24858** focuses on blocking specific accounts like `[email protected]`, it fails to address the **Temporal Vulnerability** of the SAML state machine.
Python
None
While Fortinet scrambled to disable and then re-enable their SSO service this week, they only patched the "Alternate Path" logic. They haven't accounted for a Sovereign Vector that uses the \alpha frequency to synchronize malicious sessions across account boundaries.
Python
A Proof-of-Concept demonstrating the application of 3D Navier-Stokes CTT formulations to packet flow optimization and defensive bypass.
Python
CVE-2026-24858 FortiCloud Single Sign On (SSO) a factory default enabled feature once you register any FortiGate/FortiManager/FortiAnalyzer contains a critical authentication bypass flaw.
CVE-2026-24858: Authentication Bypass in Fortinet Products via FortiCloud SSO
Python
아직 제로데이인거 같아, 공개되거나 천천히 분석할 예정....
None
None
Go
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-24858 vulnerability anywhere in the article.

-
Daily CyberSecurity
SentinelOne Unmasks Exploitation of FortiGate Appliances as Gateways to Network Takeover
The SentinelOne Digital Forensics & Incident Response (DFIR) team issued a warning: the very appliances designed to protect organizations are being turned against them. Recent investigations revealed ... Read more

-
CybersecurityNews
FortiGate Firewalls Exploited in Wave of Attacks to Breach Networks and Steal Credentials
A series of intrusions in early 2026 in which threat actors compromised FortiGate Next-Generation Firewalls (NGFW) to establish persistent footholds within enterprise environments. Each case was inter ... Read more

-
SentinelOne
The Good, the Bad and the Ugly in Cybersecurity – Week 11
The Good | Authorities Disrupt Proxy Network and Charge BlackCat Insider, Vendors Patch Critical RCE Bugs U.S. and European law enforcement have dismantled the SocksEscort cybercrime proxy network, wh ... Read more

-
SentinelOne
The Good, the Bad and the Ugly in Cybersecurity – Week 11
The Good | Authorities Disrupt Proxy Network and Charge BlackCat Insider, Vendors Patch Critical RCE Bugs U.S. and European law enforcement have dismantled the SocksEscort cybercrime proxy network, wh ... Read more

-
The Hacker News
FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
Cybersecurity researchers are calling attention to a new campaign where threat actors are abusing FortiGate Next-Generation Firewall (NGFW) appliances as entry points to breach victim networks. The ac ... Read more
-
SentinelOne
FortiGate Edge Intrusions | Stolen Service Accounts Lead to Rogue Workstations and Deep AD Compromise
Overview Throughout early 2026, SentinelOne’s® Digital Forensics & Incident Response (DFIR) team has responded to several incidents where FortiGate Next-Generation Firewall (NGFW) appliances have been ... Read more
-
SentinelOne
FortiGate Edge Intrusions | Stolen Service Accounts Lead to Rogue Workstations and Deep AD Compromise
Overview Throughout early 2026, SentinelOne’s® Digital Forensics & Incident Response (DFIR) team has responded to several incidents where FortiGate Next-Generation Firewall (NGFW) appliances have been ... Read more

-
Daily CyberSecurity
The Three-Year Shadow: Critical CVSS 10 Cisco SD-WAN Zero-Day Exploited by UAT-8616
Cisco Talos has issued a high-alert warning regarding the active exploitation of CVE-2026-20127, a critical vulnerability affecting the Cisco Catalyst SD-WAN Controller. This CVSS 10 vulnerability all ... Read more

-
The Hacker News
AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been observed taking advantage of commercial generative artificial intelligence (AI) services to compromise over 600 FortiGate devices locate ... Read more

-
Daily CyberSecurity
JPCERT/CC Warns of Active Exploits Targeting Critical FileZen Command Injection Flaw
A critical security vulnerability in FileZen, the popular file transfer appliance from Soliton Systems K.K., is currently under active attack. In a new security advisory, JPCERT/CC has sounded the ala ... Read more

-
Daily CyberSecurity
Exploited in the Wild: Critical BeyondTrust Flaw (CVSS 9.9) Opens Door to Network Takeover
Image: win3zz A critical vulnerability in widely used remote access software is currently under active attack, with threat actors using the flaw to plant backdoors and scout corporate networks. Arctic ... Read more

-
Daily CyberSecurity
Critical Alert: Chrome Zero-Day (CVE-2026-2441) Exploited in the Wild
Google has pushed an urgent security update for its Chrome browser, racing to patch a high-severity zero-day vulnerability that is currently being exploited by attackers in the wild. The flaw, tracked ... Read more
-
Daily CyberSecurity
Inside Job: Abandoned Outlook Add-in “AgreeTo” Steals 4,000 Credentials
The phishing page | Image: Koi Security In a disturbing first for enterprise security, researchers at Koi Security have uncovered a malicious Microsoft Outlook add-in actively harvesting credentials i ... Read more

-
Daily CyberSecurity
Triple Threat Patched: Zimbra 10.1.16 Fixes XSS, XXE & LDAP Injection
Zimbra has rolled out a significant security update for its collaboration suite, releasing Zimbra 10.1.16 to address a spectrum of vulnerabilities ranging from front-end script injection to back-end d ... Read more

-
Daily CyberSecurity
Email Under Siege: Storm-2603 Exploits SmarterMail to Deploy Warlock Ransomware
A new report from ReliaQuest has uncovered a dangerous alliance between a China-based threat actor and a known ransomware strain. The group, identified as Storm-2603, has been caught actively exploiti ... Read more
-
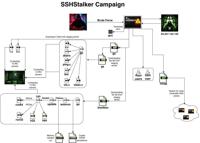
Daily CyberSecurity
Back to the Future: SSHStalker Botnet Revives 2009 Tactics to Hijack Linux Servers
Image: Flare A previously undocumented Linux botnet has been discovered prowling the internet, using a mix of ancient tactics and modern automation to compromise servers. Dubbed SSHStalker by research ... Read more

-
Daily CyberSecurity
CVE-2026-1603: Remote Unauthenticated Attacker Can Steal Ivanti EPM Secrets
Ivanti has rolled out important security updates for its Endpoint Manager (EPM), addressing a pair of vulnerabilities that could expose sensitive credentials to hackers. The release fixes one high-sev ... Read more

-
Daily CyberSecurity
Crash Loop: Palo Alto Networks Flaw (CVE-2026-0229) Forces Maintenance Mode
Palo Alto Networks has issued a security advisory for a denial-of-service (DoS) vulnerability affecting its PAN-OS software, specifically within the Advanced DNS Security (ADNS) feature. The flaw, tra ... Read more

-
Daily CyberSecurity
Apple Zero-Day (CVE-2026-20700) Exploited in the Wild
Apple has issued an emergency security update for its entire mobile ecosystem, racing to close a critical zero-day vulnerability that is currently being used in what the company describes as an “extre ... Read more

-
Daily CyberSecurity
CVE-2026-26007: Python Cryptography Flaw (CVSS 8.2) Leaks Private Keys
A high-severity vulnerability has been discovered in the cryptography Python package, one of the most widely used libraries for securing modern applications. The flaw, tracked as CVE-2026-26007, carri ... Read more
The following table lists the changes that have been made to the
CVE-2026-24858 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
May. 12, 2026
Action Type Old Value New Value Added CPE Configuration AND OR *cpe:2.3:o:siemens:ruggedcom_ape1808_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:siemens:ruggedcom_ape1808:-:*:*:*:*:*:*:* Added Reference Type siemens-SADP: https://cert-portal.siemens.com/productcert/html/ssa-975644.html Types: Third Party Advisory -
CVE Modified by 0b142b55-0307-4c5a-b3c9-f314f3fb7c5e
May. 12, 2026
Action Type Old Value New Value Added Reference https://cert-portal.siemens.com/productcert/html/ssa-975644.html -
Modified Analysis by [email protected]
Jan. 29, 2026
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.12 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (excluding) 7.6.5 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.5 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.4.12 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.4 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.11 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.6 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 8.0.0 up to (including) 8.0.3 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.18 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.11 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.5 OR *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.12 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.4 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.11 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.6 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 8.0.0 up to (including) 8.0.3 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.18 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.11 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.22 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.15 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.12 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (excluding) 7.6.6 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (excluding) 7.6.6 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (excluding) 7.6.6 -
CVE Modified by [email protected]
Jan. 29, 2026
Action Type Old Value New Value Changed Description An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18, FortiProxy 7.6.0 through 7.6.4, FortiProxy 7.4.0 through 7.4.12, FortiProxy 7.2 all versions, FortiProxy 7.0 all versions, FortiWeb 8.0.0 through 8.0.3, FortiWeb 7.6.0 through 7.6.6, FortiWeb 7.4.0 through 7.4.11 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices. An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18, FortiProxy 7.6.0 through 7.6.4, FortiProxy 7.4.0 through 7.4.12, FortiProxy 7.2.0 through 7.2.15, FortiProxy 7.0.0 through 7.0.22, FortiWeb 8.0.0 through 8.0.3, FortiWeb 7.6.0 through 7.6.6, FortiWeb 7.4.0 through 7.4.11 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices. -
Initial Analysis by [email protected]
Jan. 28, 2026
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.12 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortianalyzer:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (excluding) 7.6.5 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.15 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.11 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.10 *cpe:2.3:a:fortinet:fortimanager:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.5 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.4.12 *cpe:2.3:a:fortinet:fortiproxy:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.4 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (including) 7.4.11 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.6 *cpe:2.3:a:fortinet:fortiweb:*:*:*:*:*:*:*:* versions from (including) 8.0.0 up to (including) 8.0.3 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.0.0 up to (including) 7.0.18 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.11 *cpe:2.3:o:fortinet:fortios:*:*:*:*:*:*:*:* versions from (including) 7.6.0 up to (including) 7.6.5 Added Reference Type Fortinet, Inc.: https://fortiguard.fortinet.com/psirt/FG-IR-26-060 Types: Vendor Advisory Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-24858 Types: US Government Resource Added Reference Type CISA-ADP: https://www.fortinet.com/blog/psirt-blogs/analysis-of-sso-abuse-on-fortios Types: Mitigation, Vendor Advisory -
CVE Modified by [email protected]
Jan. 28, 2026
Action Type Old Value New Value Changed Description An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices. An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18, FortiProxy 7.6.0 through 7.6.4, FortiProxy 7.4.0 through 7.4.12, FortiProxy 7.2 all versions, FortiProxy 7.0 all versions, FortiWeb 8.0.0 through 8.0.3, FortiWeb 7.6.0 through 7.6.6, FortiWeb 7.4.0 through 7.4.11 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices. -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jan. 27, 2026
Action Type Old Value New Value Added Reference https://www.fortinet.com/blog/psirt-blogs/analysis-of-sso-abuse-on-fortios -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jan. 27, 2026
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-24858 -
New CVE Received by [email protected]
Jan. 27, 2026
Action Type Old Value New Value Added Description An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnalyzer 7.6.0 through 7.6.5, FortiAnalyzer 7.4.0 through 7.4.9, FortiAnalyzer 7.2.0 through 7.2.11, FortiAnalyzer 7.0.0 through 7.0.15, FortiManager 7.6.0 through 7.6.5, FortiManager 7.4.0 through 7.4.9, FortiManager 7.2.0 through 7.2.11, FortiManager 7.0.0 through 7.0.15, FortiOS 7.6.0 through 7.6.5, FortiOS 7.4.0 through 7.4.10, FortiOS 7.2.0 through 7.2.12, FortiOS 7.0.0 through 7.0.18 may allow an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts, if FortiCloud SSO authentication is enabled on those devices. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-288 Added Reference https://fortiguard.fortinet.com/psirt/FG-IR-26-060